How To Mount BitLocker-Encrypted Windows Partitions On Linux
This is a guide on how to access a BitLocker-encrypted Windows volume from Linux, useful in cases of dual-booting Windows 10, 8 or 7, and a Linux distribution. It covers how to decrypt and mount the BitLocker partition from the command line, as well as how to add it to
/etc/fstab, so it's automatically mounted on boot.BitLocker is the logical volume encryption system included with Microsoft Windows. BitLocker is available in the Pro and Enterprise editions of Windows 10, 8, and 8.1, as well as in the Education editions of Windows 10. It's also available for the older Windows 7 and Vista Ultimate and Enterprise.
To decrypt and mount BitLocker volumes we'll use Dislocker, a tool for reading BitLocker encrypted partitions on Linux and macOS. Dislocker features read/write support for BitLocker encrypted partitions on Windows 10, 8.1, 8, 7 and Vista (AES-CBC, AES-XTS, 128 or 256 bits, with or without the Elephant diffuser). It also supports BitLocker-To-Go encrypted partitions (USB/FAT32 partitions).
1. Install Dislocker
- Debian, Ubuntu (starting with Ubuntu 18.04), Linux Mint (starting with Linux Mint 19), elementary OS (5.0 Juno +), and other Debian or Ubuntu based Linux distributions:
sudo apt install dislockerThere's also a Dislocker PPA for Ubuntu 16.04 and 14.04 / Linux Mint 18.x and 17.x.
- Fedora:
sudo dnf install dislockerOn other Linux distributions search for Dislocker in the repositories. You may be able to find user-created packages as well, like this Arch Linux AUR package. There's also the option of building it from source.
2. Create two folders for decrypting and mounting the BitLocker-encrypted Windows partition
sudo mkdir -p /media/bitlocker
sudo mkdir -p /media/bitlockermount3. Identify the partition that's encrypted using BitLocker
You can use
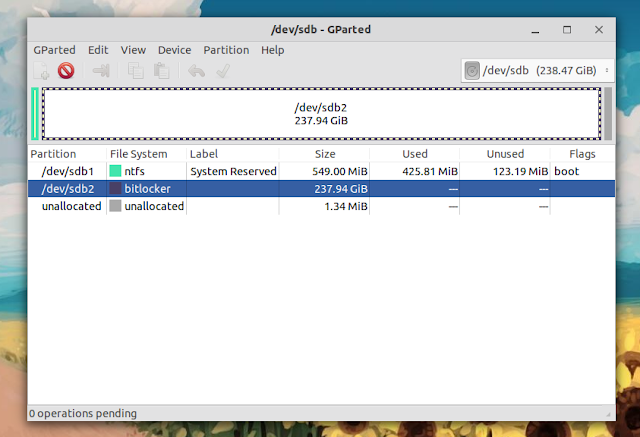
sudo fdisk -l and lsblk to see all the available partitions from the command line - you'll have to figure out which uses BitLocker encryption. Or, you could use GParted, which shows
bitlocker in the File System columns for BitLocker-encrypted partitions, so it's very easy to see the partition you're looking for:As shown in the screenshot, in my case the BitLocker-encrypted partition is
/dev/sdb2.4. Decrypt and mount the BitLocker-encrypted partition on Linux
The first command decrypts the BitLocker-encrypted filesystem, and the second command mounts it to
/media/bitlockermount:sudo dislocker <partition> -u<password> -- /media/bitlocker
sudo mount -o loop /media/bitlocker/dislocker-file /media/bitlockermountReplace
<partition> with the partition that uses BitLocker encryption (for example /dev/sda1, /dev/sdb2, etc.) which you identified in step 3, and <password> with the user password for that BitLocker volume. You can add -r to both commands to decrypt and mount it as read-only. Important: in case you get an error saying:
mount: /media/bitlockermount: wrong fs type, bad option, bad superblock on /dev/loop10, missing codepage or helper program, or other error.... when running the second command (
sudo mount -o loop /media/bitlocker/dislocker-file /media/bitlockermount), specify the filesystem type and it will work. Like this:- for NTFS (requires
ntfs-3gto be installed):
sudo mount -t ntfs-3g -o loop /media/bitlocker/dislocker-file /media/bitlockermount- for exFAT (requires the
exfat-fusepackage to be installed):
sudo mount -t exFAT-fuse -o loop /media/bitlocker/dislocker-file /media/bitlockermountInstead of the user password (
-uPASSWORD), you could also decrypt the BitLocker volume using the recovery password (-pPASSWORD), using a clear key (-c) or using the BEK file (-f BEKFILE). There is no space between
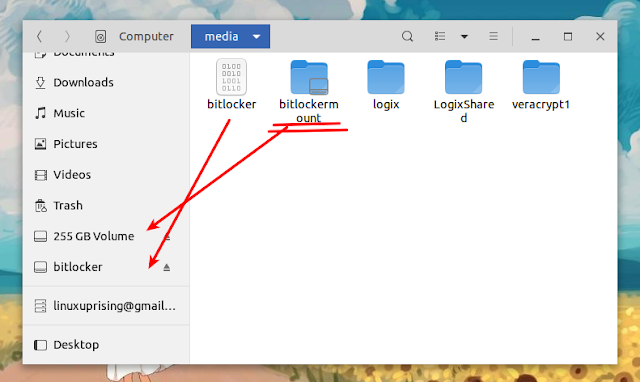
-u or -p and the password, that's not a typo!You should now be able to access your Windows BitLocker-encrypted volume from your Linux desktop. It should show up in your file manager, be available in the save as dialogs, and so on. A note that using Nautilus, you may see an extra bitlocker (/media/bitlocker) volume - ignore it. You'll find your files in
/media/bitlockermount, and not /media/bitlocker:Encryption-related:
- How To Encrypt An USB Drive With VeraCrypt (Compatible With Windows, macOS and Linux)
- How To Encrypt The Home Folder In Ubuntu 18.04
Optionally mount the BitLocker-encrypted partition on boot by adding it to /etc/fstab
If you want to have the BitLocker encrypted volume automatically mounted on boot, the Dislocker README has an example for mounting a BitLocker partition using
/etc/fstab (though incomplete - it didn't have the dislocker-file line, which I added):<partition> /media/bitlocker fuse.dislocker user-password=<password>,nofail 0 0
/media/bitlocker/dislocker-file /media/bitlockermount auto nofail 0 0Replace
<partition> with the BitLocker partition (e.g. /dev/sdb2), and <password> with the user password. You may use recovery-password instead of user-password. I assume there's also the option of authenticating this with a BEK file (bekfile option), though this is not specified in the documentation.You'll need to add these two lines (modified as mentioned above) to your
/etc/fstab file if you want to have the BitLocker-encrypted partition automatically mounted on boot. Be careful when editing the fstab file as it can easily cause your system not to boot! It's probably best to try the manual steps before adding this to your fstab file.You can edit
/etc/fstab with a console text editor, like Nano:sudo nano /etc/fstabPaste those two modified lines at the bottom, save and exit Nano (use
Ctrl + O, Enter to save, then Ctrl + X to exit), and reboot your system to try it out.